An Innovative Method of Malicious Code Injection Attacks on Websites
Main Article Content
Abstract
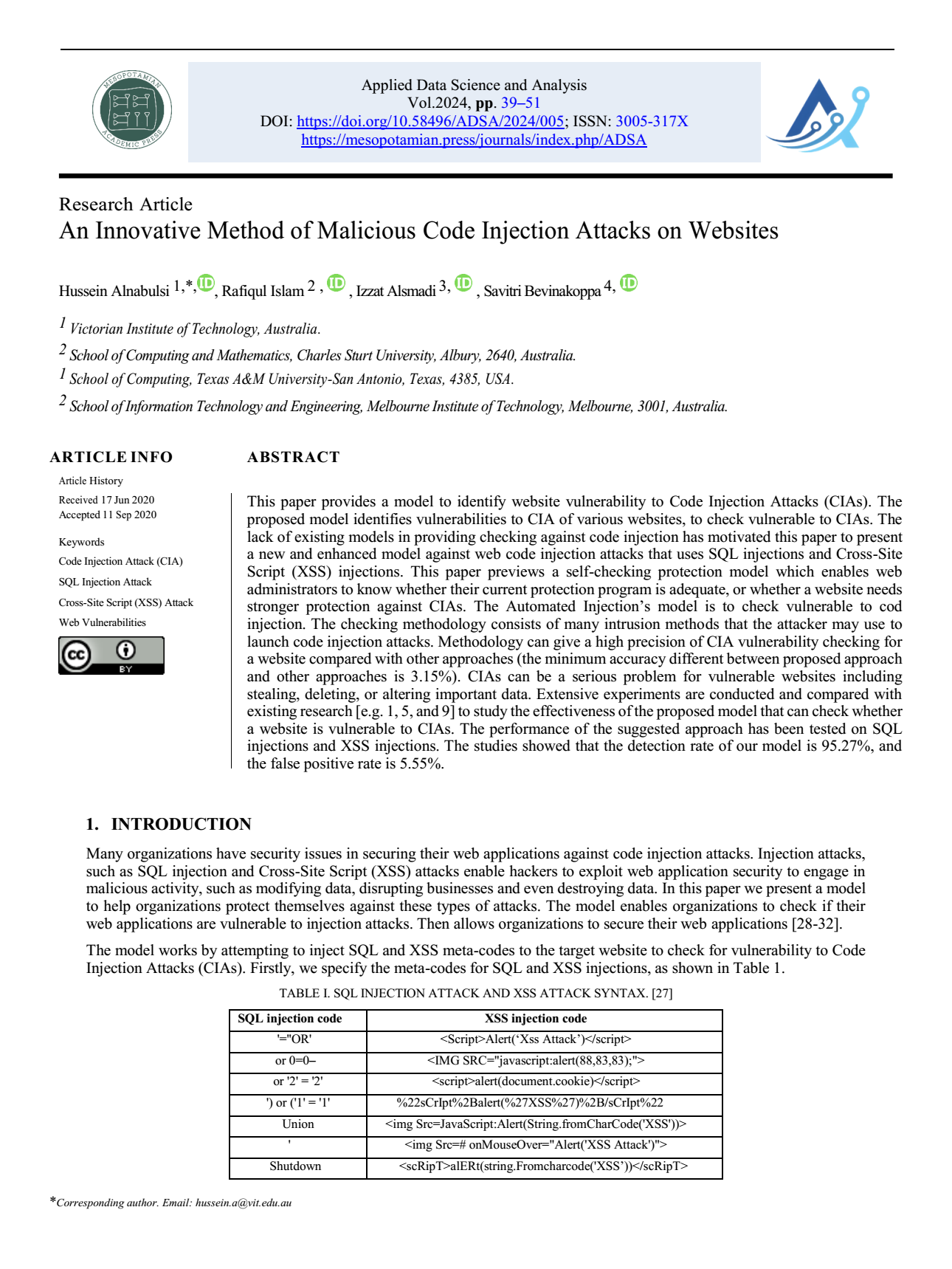
This paper provides a model to identify website vulnerability to Code Injection Attacks (CIAs). The proposed model identifies vulnerabilities to CIA of various websites, to check vulnerable to CIAs. The lack of existing models in providing checking against code injection has motivated this paper to present a new and enhanced model against web code injection attacks that uses SQL injections and Cross-Site Script (XSS) injections. This paper previews a self-checking protection model which enables web administrators to know whether their current protection program is adequate, or whether a website needs stronger protection against CIAs. The Automated Injection’s model is to check vulnerable to cod injection. The checking methodology consists of many intrusion methods that the attacker may use to launch code injection attacks. Methodology can give a high precision of CIA vulnerability checking for a website compared with other approaches (the minimum accuracy different between proposed approach and other approaches is 3.15%). CIAs can be a serious problem for vulnerable websites including stealing, deleting, or altering important data. Extensive experiments are conducted and compared with existing research [e.g. 1, 5, and 9] to study the effectiveness of the proposed model that can check whether a website is vulnerable to CIAs. The performance of the suggested approach has been tested on SQL injections and XSS injections. The studies showed that the detection rate of our model is 95.27%, and the false positive rate is 5.55%.
Article Details
Issue
Section

This work is licensed under a Creative Commons Attribution 4.0 International License.
Deprecated: json_decode(): Passing null to parameter #1 ($json) of type string is deprecated in /home/u273879158/domains/mesopotamian.press/public_html/journals/plugins/generic/citations/CitationsPlugin.php on line 68
How to Cite
References
J. Bau, E. Bursztein, D. Gupta, and J. Mitchell, "State of the art: Automated black-box web application vulnerability testing," in 2010 IEEE Symposium on Security and Privacy, pp. 332-345, IEEE, May 2010. DOI: https://doi.org/10.1109/SP.2010.27
J. Fonseca, M. Vieira, and H. Madeira, "Vulnerability & attack injection for web applications," in 2009 IEEE/IFIP International Conference on Dependable Systems & Networks, pp. 93-102, IEEE, June 2009. DOI: https://doi.org/10.1109/DSN.2009.5270349
N. Neves, J. Antunes, M. Correia, P. Verissimo, and R. Neves, "Using attack injection to discover new vulnerabilities," in International Conference on Dependable Systems and Networks (DSN'06), pp. 457-466, IEEE, June 2006. DOI: https://doi.org/10.1109/DSN.2006.72
J. Fonseca and M. Vieira, "Mapping software faults with web security vulnerabilities," in 2008 IEEE International Conference on Dependable Systems and Networks With FTCS and DCC (DSN), pp. 257-266, IEEE, June 2008. DOI: https://doi.org/10.1109/DSN.2008.4630094
J. Fonseca, M. Vieira, H. Madeira, and M. Henrique, "Training security assurance teams using vulnerability injection," in 2008 14th IEEE Pacific Rim International Symposium on Dependable Computing, pp. 297-304, IEEE, December 2008. DOI: https://doi.org/10.1109/PRDC.2008.43
J. Fonseca, M. Vieira, and H. Madeira, "Testing and comparing web vulnerability scanning tools for SQL injection and XSS attacks," in 13th Pacific Rim International Symposium on Dependable Computing (PRDC 2007), pp. 365-372, IEEE, December 2007. DOI: https://doi.org/10.1109/PRDC.2007.55
D. T. Stott, B. Floering, D. Burke, Z. Kalbarczpk, and R. K. Iyer, "NFTAPE: A framework for assessing dependability in distributed systems with lightweight fault injectors," in Proceedings IEEE International Computer Performance and Dependability Symposium. IPDS 2000, pp. 91-100, IEEE, March 2000. DOI: https://doi.org/10.1109/IPDS.2000.839467
P. Bhojak, V. Shah, K. Patel, and D. Gol, "Automated Web Application Vulnerability Detection With Penetration Testing," ICRISET2017 Volume 2, 2017. DOI: https://doi.org/10.29007/vs62
I. Medeiros, N. F. Neves, and M. Correia, "Automatic detection and correction of web application vulnerabilities using data mining to predict false positives," in Proceedings of the 23rd International Conference on World Wide Web, pp. 63-74, April 2014. DOI: https://doi.org/10.1145/2566486.2568024
H. Alnabulsi, M. R. Islam, and Q. Mamun, "Detecting SQL injection attacks using SNORT IDS," in Asia-Pacific World Congress on Computer Science and Engineering, pp. 1-7, IEEE, November 2014. DOI: https://doi.org/10.1109/APWCCSE.2014.7053873
Websmart Inc., "100000 Vulnerable Websites," available online: https://samsclass.info/125/ethics/smart-websites.htm, September 2017.
H. Alnabulsi and M. R. Islam, "Identification of susceptible websites from code injection attack," in 1st International Conference on Machine Learning and Data Engineering: iCMLDE 2017, pp. 1-9, Global Circle for Scientific, Technological and Management Research, 2017.
N. Antunes, M. Vieira, and H. Madeira, "Web Services Vulnerabilities," 2008, available online: http://eden.dei.uc.pt/~mvieir.
"The latest list of SQL injection vulnerable websites 2016," August 2017, available online: http://www.sunnytech7.com/pages/latest-2016-list-of-SQL-vulnerable-websites.html.
"Vulnerable Sites To (Legally) Practice Your Hacking Skills," August 2017, available online: https://www.checkmarx.com/2015/04/16/15-vulnerable-sites-to-legally-practice-your-hacking-skills/.
"Download Biggest SQL Vulnerable Website List For 2017," August 2017, available online: http://www.arkdots.com/sql-vulnerable-website-list/.
"150 SQL Vulnerable Websites 2017 List," August 2017, available online: https://www.scribd.com/document/325850327/150-SQL-Vulnerable-Websites-2017-List.
"List Of web sites Vulnerable For SQL Injection," August 2017, available online: http://listsql.blogspot.com.au/.
"20 famous websites vulnerable to cross-site scripting," August 2017, available online: http://thehackernews.com/2011/09/20-famous-websites-vulnerable-to-cross.html.
"Xss: XSS vulnerable sites collection," August 2017, available online: http://cyb3rninjas.blogspot.com.au/2015/03/xss-xss-vulnerable-sites-collection.html.
"10000 fresh SQLi vulnerable websites list," August 2017, available online: https://pastebin.com/ATJE7VdZ.
"Testing for Cross-site scripting," April 2018, available online: http://www.owasp.org/index/Testing_for_Cross_site_scripting.
"How To Test For Cross-Site Scripting (XSS)," April 2018, available online: https://affinity-it-security.com/how-to-test-for-cross-site-scripting-xss/.
C. S. Cheah and V. Selvarajah, "A review of common web application breaching techniques (SQLi, XSS, CSRF)," in 3rd International Conference on Integrated Intelligent Computing Communication & Security (ICIIC 2021), pp. 540-547, Atlantis Press, September 2021. DOI: https://doi.org/10.2991/ahis.k.210913.068
A. Javed, "Revisiting XSS Sanitization," ISACA Ireland Conference 2014, 2014.
H. Alnabulsi, R. Islam, and M. Talukder, "GMSA: Gathering Multiple Signatures Approach to Defend against Code Injection Attacks," IEEE Access, pp. 1-12, November 2018. DOI: https://doi.org/10.1109/ACCESS.2018.2884201
H. Alnabulsi, R. Islam, and Q. Mamun, "A novel algorithm to protect code injection attacks," in Springer International Conference on Applications and Techniques in Cyber Security and Intelligence (ATCSI), vol. 580, Springer China, 2018, pp. 281-292. DOI: https://doi.org/10.1007/978-3-319-67071-3_35
S. K. Iqbal et al., "Real-time-based E-health systems: Design and implementation of a lightweight key management protocol for securing sensitive information of patients," Health and Technology, vol. 9, pp. 93-111, 2019. DOI: https://doi.org/10.1007/s12553-018-0252-4
A. H. Mohsin et al., "Based medical systems for patient’s authentication: Towards a new verification secure framework using CIA standard," Journal of Medical Systems, vol. 43, no. 7, article 192, 2019. DOI: https://doi.org/10.1007/s10916-019-1264-y
M. L. Shuwandy et al., "mHealth authentication approach based 3D touchscreen and microphone sensors for real-time remote healthcare monitoring system: comprehensive review open issues and methodological aspects," Computer Science Review, vol. 38, article 100300, 2020. DOI: https://doi.org/10.1016/j.cosrev.2020.100300
A. Alamleh et al., "Federated learning for IoMT applications: A standardization and benchmarking framework of intrusion detection systems," IEEE Journal of Biomedical and Health Informatics, vol. 27, no. 2, pp. 878-887, 2022. DOI: https://doi.org/10.1109/JBHI.2022.3167256
M. L. Shuwandy et al., "Sensor-Based Authentication in Smartphone; a Systematic Review," Journal of Engineering Research, 2024. DOI: https://doi.org/10.1016/j.jer.2024.02.003